How to Setup SSO using Forgerock
Single Sign-On (SSO) is a user authentication process that allows your users to sign in to multiple applications using the same set of login credentials. This allows ease of use for the end users and ease of management for administrators. VIDIZMO offers the most flexible options for you to integrate with a wide range of single sign-on authentication providers, including:
- Directory services such as Azure AD etc.
- Identity Access Management (IAM) services such as Okta, OneLogin, Ping, Centrify, ForgeRock.
- Third-party login services such as Facebook, Google, Office 365, X(Twitter), LinkedIn, etc.
With an app model integration for SSO, VIDIZMO makes the integration as easy as enabling/disabling your identity provider from within the platform administrator interface in minutes. Enterprises using ForgeRock Access Management as their identity provider can utilize SSO option with VIDIZMO, allowing users to sign in using the same set of credentials.
For more information about VIDIZMO SSO Apps, read Understanding Single Sign-On.
Prerequisites
- For configuring ForgeRock SSO with VIDIZMO, you must have a ForgeRock Identity server's administrator account so that you can create a ForgeRock OAuth 2.0 application for authorization.
- If more SSO Apps have been configured and enabled on your Portal other than ForgeRock SSO, your users will see multiple buttons on the login page allowing them to choose any identity provider of their choice to log in to their VIDIZMO Portal.
- VIDIZMO requires your ForgeRock authorization server to expose a list of scopes to map attributes and provide user authentication. These scopes include:
- Profile (The user's First Name and Last Name are exposed and mapped in your VIDIZMO account in this Scope)
- Email (The user's Email Address is exposed and mapped in your VIDIZMO account in this Scope)
- Openid (this is required to indicate that the application intends to use OIDC to verify the user's identity)
- Ensure that you belong to a group where the SSO app permission is enabled to access this feature.
- If your portal is using HTTPS protocol, make sure your ForgeRock authentication server is also using HTTPS.
Configuration in ForgeRock
Configure OAuth Applications
- After you log into your ForgeRock authorization server using admin account, go to your default current realm.
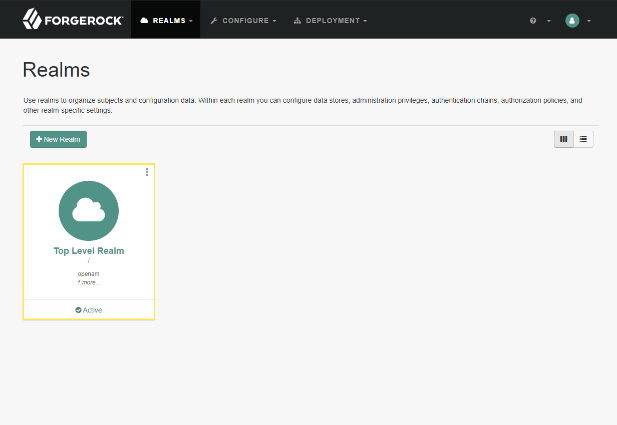
-
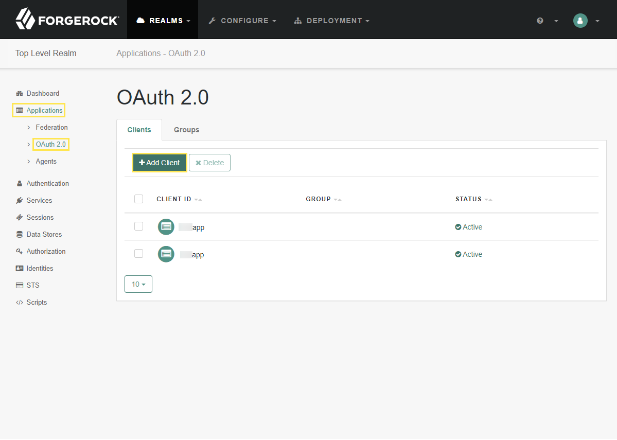
From your Realm Dashboard:
- Expand Applications from the left menu bar options.
- Select OAuth 2.0 to create an application that communicates with ForgeRock on behalf of VIDIZMO.
- Select Add Client to create your own application.
Set up OAuth 2.0 Client
-
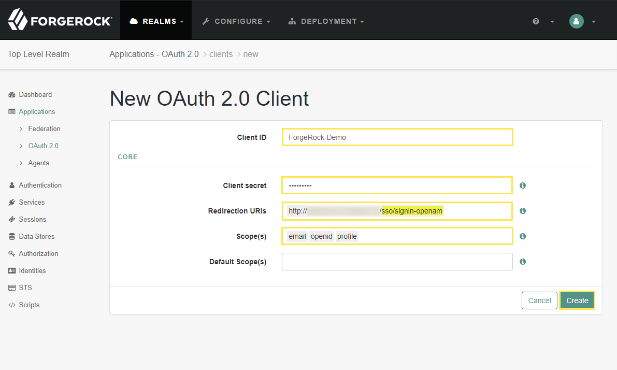
On the New OAuth 2.0 Client screen:
- Enter the name you wish to assign to the client application. For demonstration purpose, this has been set to ForgeRock-Demo. Make sure to save it for configuration in VIDIZMO Portal in the next step.
- Set the secret to your Client and save it for configuration in VIDIZMO Portal.
- Redirection URIs help ForgeRock whitelist addresses upon which to send user information after a successful login, which is why you need to enter your Portal's URL appended with
/sso/signin-openamas shown. - Next are scopes, these are the parameters that VIDIZMO would need from ForgeRock to authenticate and authorize the user to log into the portal. Here, include email, openid and profile. Read more about what information does each of them contain here.
- Select Create to proceed.
-
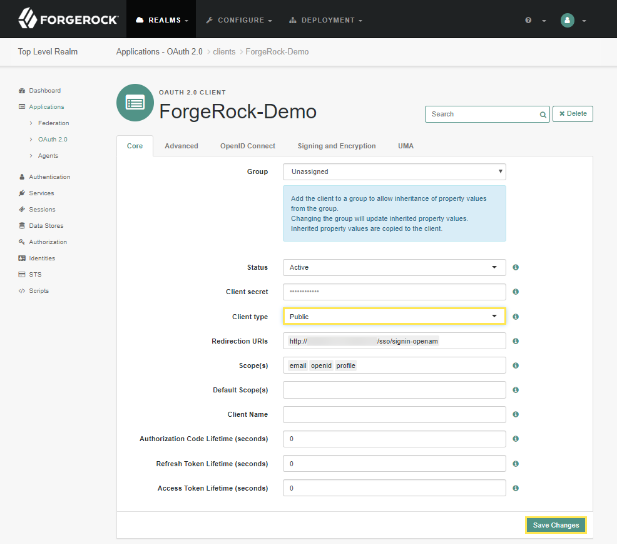
From the OAuth 2.0 Client application you just created, now you only need to make a minor change:
- Change the Client type from Confidential to Public.
- Select Save Changes.
-
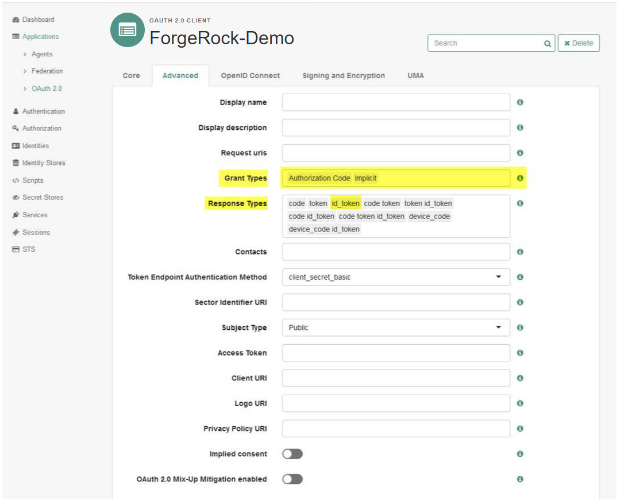
Go to the Advanced tab and make sure the following is configured:
- Under Grant Types, add Implicit.
- Similarly, in Response Types, make sure you have added id_token which is required by OAuth.
Configuration in VIDIZMO
Configure SSO Apps
-
Open the navigation menu via the button on the top left.
-
Select the Admin dropdown.
-
Select Portal Settings.
-
Select Apps.
-
Select Single Sign-On.
-
Select the settings icon on the ForgeRock Access Management app.
-
In the ForgeRock Access Management - Settings dialog, configure the following:
-
Client ID Enter the name you gave to your application while setting it up in ForgeRock.
-
Client Secret Enter the secret that you set while configuring your application.
-
Authority The ForgeRock server's URL appended with
/oauth2. -
Meta Address Metadata address for the ForgeRock server (optional).
-
Requires HTTPS Metadata Select this checkbox if your ForgeRock server uses HTTPS.
-
Callback Path The redirect URI path used after authentication. This is pre-configured to
/sso/signin-openam. -
Scope The scopes required for authentication. Pre-configured to
email,profile, andopenid. -
Force Login Select this checkbox to force users to re-authenticate each time they access the Portal.
-
Attribute Mapping Maps ForgeRock user attributes to VIDIZMO attributes. The default mappings include FirstName, LastName, EmailAddress, and ExternalSystemId.
-
CAL When a user enters the Portal via ForgeRock SSO, this CAL is assigned to them, granting the permissions associated with that CAL.
-
-
Select Save Changes.
-
Turn on the toggle to enable ForgeRock SSO on your Portal.
Sign in using ForgeRock
Sign out from your existing account and navigate back to the Login page to see an option to sign in using ForgeRock Access Management.